Should you use SMS or email for two-factor authentication?
Two-factor authentication (2FA) adds an additional layer of protection beyond passwords. Here we take a look at the pros and cons of the two most common authentication methods.

Two-factor authentication (2FA) adds an additional layer of protection beyond passwords. Here we take a look at the pros and cons of the two most common authentication methods.

While the tech behind 2FA is decades old, it’s only in the last few years that it’s become mainstream.
It’s easy to see why this additional layer of security has become so popular.
2FA is simple enough for most people to understand and implement–all while being highly effective. (For example, it would have prevented one of the biggest political scandals in American history.)
With its rise in adoption, there’s growing debate on what the best authentication method is.
If you want a simple guide to the advantages and disadvantages of email and SMS for your 2FA system, this article is for you. We’ll take a look at:
Most online services and computer systems only require single-factor authentication. That is a username and password combination.
With two-factor authentication, your customers or users need to provide both a password/username and prove their identity in some other way to gain access.
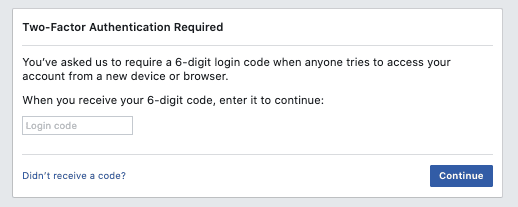
For example, if you try to log into Facebook from a new device or browser you’ll be greeted with this message.
You then use a second factor to prove it’s you attempting to log in. There are typically three types of authentication factors:
When someone tries to log in to an account, they automatically receive an SMS message to their phone number with a unique authentication code. This code is then inputted by you, verifying your authorization and granting access.
Research from Google shows that adding a recovery phone number to your Google Account can block up to 100% of automated bots, 99% of bulk phishing attacks, and 66% of targeted attacks that occurred during their investigation.
Apart from being effective, one of the major benefits of SMS 2FA is that it does not require another app or any additional setup to configure. Texting also benefits from:
2FA email follows the same process as 2FA SMS, but you receive a code to your email address instead of a text message.
One of the major benefits of using email is that people are already comfortable providing their email address to online services.
Plus, like SMS, many people already have their email open on their computer or their mobile device, so accessing email is also highly convenient.
The problem with using email as a 2FA delivery channel is that the first layer of security–a password–can usually be reset from an email account.
That means if someone compromises your email inbox, they can take over all your online accounts using the 2FA codes they send themselves.
Since a hacker would need access to a person’s cellphone, SMS is often considered more secure.
But, with that being said, 2FA SMS is not impenetrable.
For example, hackers can use social engineering to gather enough information to pull off a SIM swap. SIM swapping occurs when someone contacts your wireless carrier and is able to convince the call center employee that they are, in fact, you.
Like a lot of security measures, whether or not it’s appropriate to use SMS as a delivery channel for 2FA will depend on your customers and the type of information you’re trying to protect.
With financial services like Paypal and Chase Bank using 2FA text messages, they’re an appropriate approach for the vast majority of use case
While not without its vulnerabilities, multi-factor authentication is an easy way to make your online service more secure.
Email 2FA remains the most unsecure of all the approaches, simply because an email address is not tied to a specific device and it’s possible to compromise a large number of accounts once you have someone’s email password.
While not perfect, 2FA SMS is the most popular solution for a reason: it’s easy to implement, affordable, and, most importantly, it works the majority of the time.
📖 Read next:
Drew Wilkinson is the Head of Marketing at SimpleTexting. Drew has more than a decade of experience managing successful integrated marketing programs to build brands, raise awareness, and generate demand.
More Posts from Drew WilkinsonLearn how ViewSpark integrates with SimpleTexting's API to help nonprofits increase donor retention, reactivation, and monthly gift amount.
ReadWhether you're considering integrating an SMS API into your platform or want to text-enable your sales or customer support team, this article will provide you with some options and ideas to get started.
ReadStart a text marketing campaign or have a 1-on-1 conversation today. It's risk free. Sign up for a free 14-day trial today to see SimpleTexting in action.
No credit card required